We investigate the contemporary example of the lna2u9h2f1k7 that attracts people online as a random set of digital strings. These codes nowadays emerge unexpectedly, become viral, and cause mass debate. Thus, it is important to know how and where they are contained. We do not speculate but concentrate on what can be seen, on technical logic, and in the real world. This gives the readers some clarity as opposed to confusion.
The digital culture is based on curiosity. As a result, a short alphanumeric string appearing in isolation becomes of great interest quickly. This is because this article is a critical and objective study of the phenomenon, in plain language and organized arguments.
lna2u9h2f1k7 in Digital Context
Lna2u9h2f1k7 may seem at first sight to be an odd garble of letters and numbers. This is normally found in software systems. They are often used by developers as short-term identifiers, placeholders or internal identifiers. Thus, the construction does not predict the threat or the covertness.
On top of that, these strings tend to have no semantic meaning. They never play linguistic functions but functional functions. Due to this, randomness is often taken out of context due to a misinterpretation by many users. Indeed, in practice such designs are frequently motivated by efficiency.
Why lna2u9h2f1k7 Attracts Online Attention
The focus on lna2u9h2f1k7 increases because of uncertainty. Patterns are something that human beings pursue.
- When clear information is missing, speculation quickly fills the gap.
- Online repetition often turns uncertainty into perceived meaning.
- Social media platforms amplify discussions around unresolved topics.
- Curiosity spreads faster than fact-checking in internet culture.
- As a result, similar codes or terms trend repeatedly without verification.
Technical Possibilities Behind lna2u9h2f1k7
Technically, lna2u9h2f1k7 belongs to some known categories. It might serve as a session token, database key or internal reference string. It is however longer and therefore standard cryptographic hashes such as MD5 or SHA variants are excluded.
Nevertheless, identifiers are commonly truncated to improve speed and readability by the developers. Thus, it is possible to find shortened strings in logs, test environments and light applications. Purpose is normally dictated by context.
Comparing Short Codes With Standard Identifiers
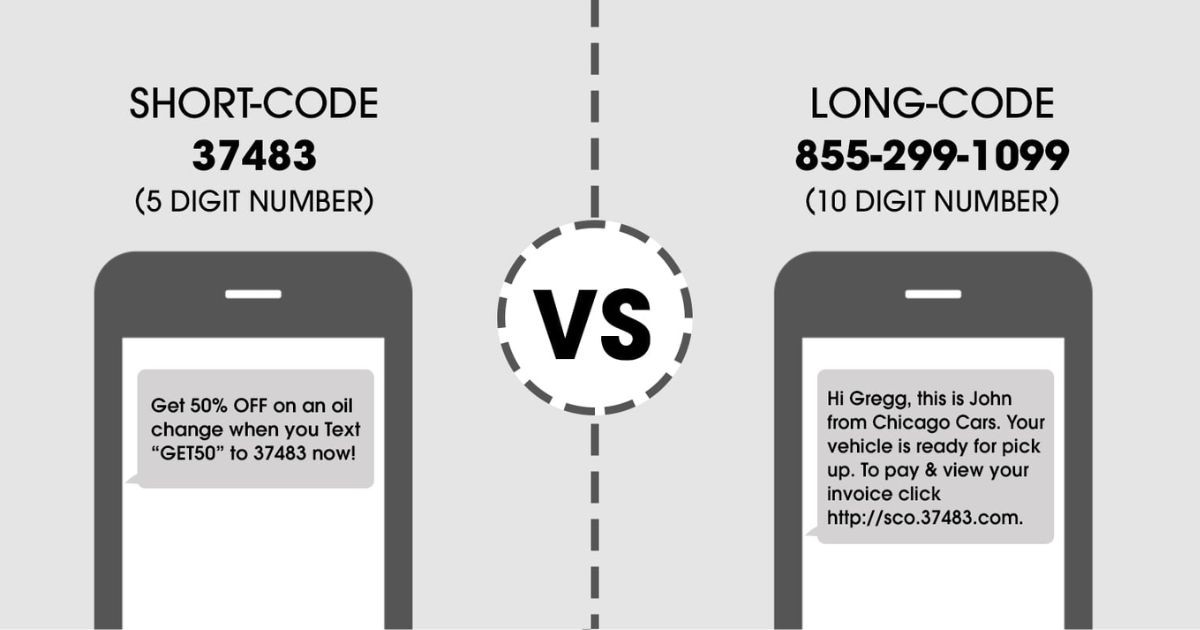
To understand such strings better, comparison helps. Standard identifiers follow predictable lengths and formats. Shorter strings prioritize efficiency over security. Consequently, they appear frequently in non-critical systems.
Identifier Comparison
| Identifier Type | Typical Length | Purpose |
| MD5 Hash | 32 characters | File integrity |
| SHA-1 Hash | 40 characters | Security validation |
| Session Token | 8–16 characters | Temporary access |
| Random String | Variable | Internal reference |
This comparison shows that short codes align more closely with internal identifiers than with security hashes.
Common Theories and Their Practical Limits
There are a number of theories that revolve around mysterious strings. There are those users who indicate the presence of hidden messages and those who think of sophisticated encryption. Such assumptions are hardly supported by practical software development, however.
Rather, the developers prefer simplicity. Randomized strings minimize the risks of duplication with no complexity. Thus, the majority of the unexplained codes are discovered to be mere artifacts and not secrets.
Real-World Examples of Similar Digital Strings
There are numerous examples in technology history. Short alphanumeric values are also seen in log files.
| Aspect | Explanation |
| Gaming Systems | Use internal tests and test codes during development and updates |
| Cloud Systems | Generate temporary IDs to track user sessions and activity |
| Source of Mystery | Often arises due to lack of information, not deliberate secrecy |
| Role of Context | Once context is provided, confusion around similar terms disappears |
| Misinterpretation | Homonyms or codes seem mysterious only when details are missing |
How to Evaluate Unknown Digital Codes Safely
After users face the unknown strings, they must be calm and systematic. To begin with, observe the location of the string. Speculation can be seen in the context more than in speculations. Second, make sure that the string is replicated across systems. Consistency is little more than a functional role.
Also, known formats can be recognized by trusted online tools. But this is not to say that users should not find unverified websites that are related to the decoder. Security measures rely on educated fear and not curiosity in the form of clicking.
Psychology Behind Online lna2u9h2f1k7 Code Fascination
The curiosity about mysterious strings is a manifestation of the human mind. Individuals like puzzles and group secrets. This practice is empowered by online communities which reward discussion and interaction.
Moreover, previous online incidents had taught people to distrust the significance. Consequently, even such innocent strings lead to investigation. Knowledge of this state of mind will enable one to dissociate entertainment and evidence.
When Randomness Becomes Viral
Importance is not a prerequisite of virality. Visibility is motivated by timing, repetition and curiosity. Search activity goes up once there are several users talking on a string. Thus, algorithms increase exposure.
This is the cycle of the neutral digital aspects becoming trending topics. The knowledge of this process stimulates critical examination rather than supposition.
lna2u9h2f1k7 Practical Takeaways for Readers
The most valuable aspect to the readers is the application of structured thinking.
- Not every unknown string needs deep interpretation or hidden meaning.
- Often, the function of a digital element explains its appearance.
- Strong technical understanding reduces unnecessary concern and confusion.
- Users can assess digital artifacts logically by observing context and usage.
- Factors like string length and repetition patterns provide useful clues.
Conclusion
Online space creates a great number of identifiers every day. A majority of them are of simple uses and vanish into obscurity. Sometimes the attention is obtained thanks to the timing and interest. Knowledge of this fact gives strength to users. Informed observation offers confidence as opposed to seeking mystery. Digital literacy converts any uncertainty into knowledge.
Also Read About: Antivirus Reedoor2.4.6.8 – Security, Features, and Performance
